Did You Know?
When your devices become infected with malware, information is the target. This is true whether it is your own information at risk or the information of others through the control of your device.
The University of North Alabama has several safeguards in place in order to protect the information of students and employees, but ultimately we are each responsible for securing our own information. 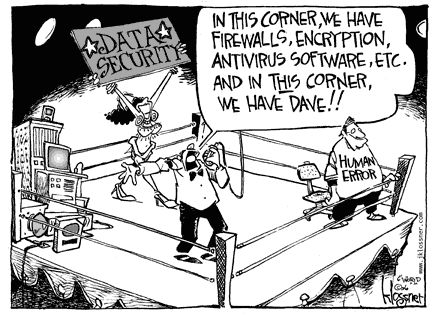 For example, UNA can enforce relatively strong passwords, but a strong password is only one piece of the information security process. If that password is shared, it may not matter how many strong password techniques it employs.
For example, UNA can enforce relatively strong passwords, but a strong password is only one piece of the information security process. If that password is shared, it may not matter how many strong password techniques it employs.
New threats to information emerge regularly, but there are several steps you can take that will greatly lower your information risks.
Take Control
Keeping systems up to date and scanning for malware regularly are some of the easiest way to reduce risk, and contrary to popular belief, this is true regardless of the type of device you use - Macs are vulnerable too. Check out our Tips page for a list of actions you can take to protect your devices, and ultimately, your information.
Basic Information Security Definitions
Below are definitions and examples of some general Information Security buzzwords that may be helpful when discussing or searching for more information about how to protect your information.
- Adware - software specifically designed to show you more ads. If you seem to be getting an excessive number of pop-up advertisements while using your device, it may be infected with adware.
- Antivirus (AV) software - type of program that searches a device or drive for known or potential viruses. AV programs need to be updated regularly in order to maintain a current database of known viruses.
- Authentication - the process of determining whether someone or something is, in fact, who or what it is declared to be. Common authentication methods include passwords, passcodes, PIN numbers, and fingerprint swipes, among others.
- Back up (verb) - to make a digital copy of your files.
- Backup (noun) - a digital copy of your files. This copy can be saved on the same device as the original or on a flash drive, external hard drive, network drive, or in cloud-based storage, and can be used to restore your data if the original becomes infected or corrupt.
- Configure - to choose specific options when installing software or changing settings on your device.
- Data corruption - the failure of digitally stored information as a result of something external to the data itself, whether hardware failure, software failure, or malware.
- Denial of service (DoS) - an attack in which a user or organization cannot access a service or resource, usually caused by an excessive amount of requests for that service or resource.
- Drive-by download - a program that is automatically downloaded to your computer without consent. These downloads can be started by visiting a Web site or viewing an HTML e-mail message, and if your device's security settings are too low, you may never see the download take place.
- Encryption - the process of changing text from readable information to make it unreadable without a password or key.
- Firewall - part of a computer or network designed to block unauthorized access.
- Flash drive - small storage device that plugs into a USB port. Flash drives are alternately referred to as thumb drives, pen drives, and USB drives.
- Malware - software that is designed to damage or disable devices or systems, or cause harm to a computer user.
- Personally identifiable information (PII) - any data that could be used on its own or with other information to identify an individual. Examples of PII include: social security number (SSN), home address, vehicle registration information, phone numbers, date of birth, credit card number, among others.
- Phishing - attempting to get information that can be used for identity theft, such as usernames, passwords, and credit card details by pretending to be a trustworthy individual or organization. Phishing attacks can take place through email, instant messaging, a web site or telephone call.
- PUP or Potentially Unwanted Program - a program that may be unwanted, whether or not it was downloaded and installed intentionally. PUPs include spyware and adware and are often downloaded in conjunction with a desired program.
- Rootkit - a collection of programs that, once installed by other means, allow for administrator-level access to a computer or network.
- Social engineering - pretending to be someone else in order to trick people into breaking normal security procedures. These attacks can happen in person or online, for example through email or social media. Types of social engineering attacks include phishing and spam, among others.
- Spam - unsolicited junk email.
- Spam filter - program designed to detect junk email and prevent it from reaching your inbox.
- Spyware - a type of malware designed to collect information by “spying” on the user.
- Trojan - a type of malware that looks like something useful or fun, but carries with it something malicious.
- Virus – a type of malware that spreads by attaching itself to a file or program that gets shared, frequently through email or USB drives. Viruses almost always corrupt or modify files.
- Vulnerability – a weakness in a computer that allows an attacker to make unauthorized changes. Vulnerabilities include weak passwords, poor configuration, or software bugs.
- Worm – a type of malware that can move on its own from computer to computer. Unlike a virus, it does not need to attach itself to a file or program in order to be spread.